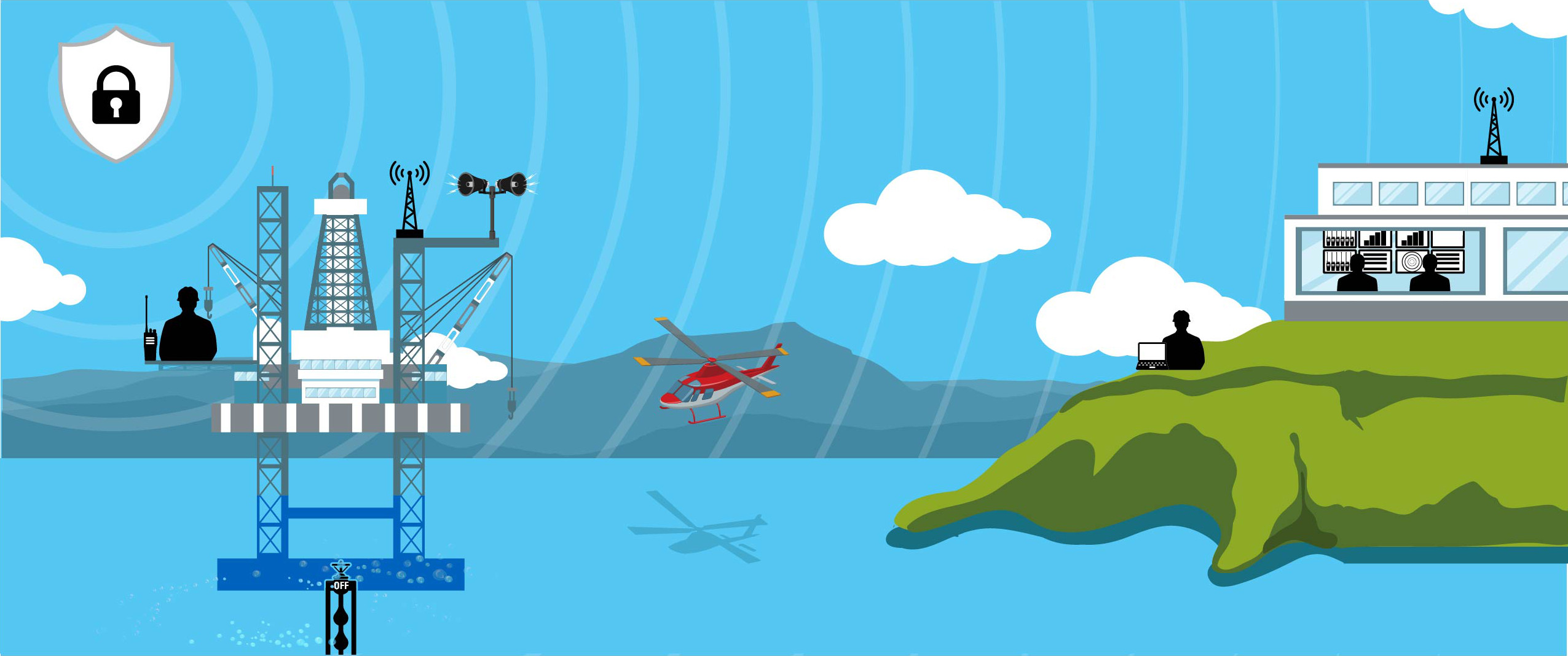
9:13:36: Crew Member Makes Emergency Call
9:13:36: Radio ID And Fleet Maps Harmonized For Rig Personnel
9:14:16: Siren Activation System To Alert Facility Personnel
9:15:01: Emergency Shutdown Activated
9:16:21: Notify Onshore Duty Emergency Coordinator
9:17:04: Alert And Activate Emergency Response Team
10:49:15: Incident Logs Collated for Analysis